Originally posted here
Touchscreen-based self-service technology is changing the way we do business, but one of the key challenges to widespread adoption is finding a way to make that technology useable by everyone.
Self-Service For All – ADA feature
By Richard Slawsky contributor
Interactive touchscreens are quickly becoming a key player in the kiosk world. Businesses ranging from fast-casual restaurants to health care facilities and mall makeup stores are finding uses for touchscreen-based kiosks, offering services ranging from food ordering to patient check-in to complexion matching.
The latest of the many reports forecasting the growth of the kiosk industry predicts the market will increase at a 9.7 percent compound annual growth rate, reaching $88.3 billion by 2022 from $46.1 billion in 2015. Drivers of that growth include increased customer’s interest towards self service, development in the retail and entertainment industries and innovations in touchscreen display and glass technology. The retail industry holds the lion’s share of the market, with about 40 percent of the overall revenue.
The growth of touchscreen-based self service hasn’t been without its challenges, though. Foremost among them has been the issue of making that technology available to all users, including those with disabilities. Another has been the expanded form factors such as tablets on the low end and large 85-inch touchscreens on the high side. That’s a shift from the mostly 17-inch and 19-inch screens that dominate the ATM, airline and POS self-checkout precursor worlds.
The compliance conundrum
The U.S. Census Bureau estimates that about 19 percent of the country’s population, or about 57 million people, have some form of disability. Those include 8.1 million people who have difficulty seeing, including 2 million who were blind or unable to see. In addition, about 7.6 million people have impaired hearing. Roughly 30.6 million have problems walking or climbing stairs, or use a wheelchair, cane, crutches or walker, and 19.9 million people had challenges lifting and grasping. This includes difficulty lifting an object or grasping a pencil (or pressing buttons on a touchscreen interface).
To ensure those with disabilities can enjoy the same rights as everyone, in 1990 Congress passed the Americans with Disabilities Act (ADA). The law was designed to afford protections against discrimination similar to those of the Civil Rights Act of 1964. According to the U.S. Department of Labor, the ADA prohibits discrimination against people with disabilities in several areas, including employment, transportation, public accommodations, communications and access to state and local government programs and services.
For a business that incorporates kiosks into its operations, that generally means that a kiosk needs to be useable by all of its customers, no matter what their physical challenges may be. In many cases meeting that standard is easier said than done.
“ADA concerns are pretty much the same concerns that one would have for any type of a consumer self-service interactive solution,” said Ron Bowers, senior vice president of business development at Grafton, Wisconsin-based kiosk vendor Frank Mayer & Associates. “Some individual deployments are only adhering to the accessibility-by-wheelchair aspect.”. “Some individual deployments are only adhering to the accessibility-by-wheelchair aspect.”
Unfortunately, those basic accommodations can result in a business overlooking more than 35 million potential customers.
It’s worth noting that a large percentage of customers in wheelchairs also suffer from physical impairment.
Some of the biggest challenges kiosk deployers face is the degree of interpretation that must be applied to some of the regulations. How many accessible units and what level of accessibility constitutes acceptable access? Another is new regulations and retrofitting existing units can be problematic, said Craig Keefner, manager for Olea Kiosks.
“Complicating retrofits can be the issue of recertifying for UL,” Keefner said. “One change to the overall machine can require the new configuration to be recertified. If Walmart has to change all of its self-checkouts, that’s a big change.”
To help add clarity to exactly what kiosk deployers must do to be ADA compliant, in mid-September the Architectural and Transportation Barriers and Compliance Board released a final rule for electronic and information technologies used by federal agencies as well as guidelines for customer premises equipment and telecommunications equipment, including kiosks. The Access Board is an independent federal agency devoted to accessibility for people with disabilities.
A sample of the guidelines for kiosks outlined in the Access Board rule
- In general, devices with a display screen shall be speech-output enabled for full and independent use by individuals with vision impairments.
- Speech output shall be provided for all information displayed on-screen.
- Where speech output is required, braille instructions for initiating the speech mode of operation shall be provided.
- Devices that deliver sound, including required speech output, shall provide volume control and output amplification.
- At least one mode of operation shall be operable with one hand and shall not require tight grasping, pinching, or twisting of the wrist. The force required to activate operable parts shall be 5 pounds (22.2 N) maximum.
|
The final rule is listed in the Federal Register. Covered organizations must meet compliance standards by Jan. 18, 2018.
Although much of the language in the final rule will likely keep lawyers busy for years to come, there are some guidelines that are easy to interpret. In general, the rules say that the technology with a display screen shall be speech-output enabled for full and independent use by individuals with vision impairments. Input controls shall be operable by touch and tactilely discernible without activation.
Running the risk
Missing out on revenue from millions of customers with disabilities is just one of the pitfalls of not complying with ADA regulations, or at least making every effort to make sense of the standards.
For violations that occurred after April 28, 2014, the maximum civil penalty for a first violation of ADA regulations is $75,000. For a subsequent violation, the maximum civil penalty is $150,000.
In addition, self-service kiosks are increasingly a target for ADA lawsuits. In March 2017, for example, the American Council of the Blind filed a lawsuit in the U.S. District Court for the Southern District of New York against fast casual restaurant chain Eatsa on behalf of a blind customer. Under Eatsa’s business model, customers order from tablet-based kiosks and pick up their food from a cubicle when it’s ready.
Customer Michael Godino claims he was unable to use a self-order kiosk in an Eatsa to place an order because the kiosks weren’t accessible for blind customers.
“Because the self-service mobile applications, touchscreen tablets, and visually-marked cubbies Eatsa utilizes rely on exclusively visual displays and do not provide any form of audio output or tactile input, Eatsa’s design is entirely inaccessible to blind customers,” according to the lawsuit.
Restaurants aren’t the only businesses open to ADA lawsuits. A proposed class action suit against mall operator Simon Property Group claims a Proactiv skincare products kiosk, located in the Simon-run Miami Mall in Florida, discriminates against blind and visually impaired individuals. The lawsuit argues the Proactiv automated retail kiosk, which uses a touchscreen display, doesn’t offer a way for blind consumers to purchase its products.
“Sighted customers can independently browse, select, and pay for Proactiv brand skincare products at the Miami Mall Proactiv kiosk. However, blind customers are denied the opportunity to participate in this retail service,” the complaint reads. “Moreover, [the defendant] has failed to provide an alternative channel for blind customers to enjoy the retail service provided through the Proactiv kiosk, such as the training of qualified readers to assist visually impaired and blind customers.”
There are about 1,000 Proactiv kiosks in malls in the United States, Canada and Japan.
And just in case a business operator thinks having a staff member on hand to assist disabled customers with using self-service technology, chances are that’s not enough to keep from running afoul of the ADA.
“It depends on the application and if the assistant is as available as the kiosk to provide services,” said Adam Aronson, CEO of San Rafael, Calif.-based Lilitab Tablet Kiosks. Lilitab designs, engineers and markets a range of tablet kiosk products. “If the cashier typically has longer lines than the kiosk, that’s not the same service level,” Aronson said.
While lawsuits against kiosk deployers related to ADA compliance are always a concern, other dangers include the negative publicity from being perceived as a business that is insensitive to the needs of disabled customers. Just a few months ago cable news was filled images of U.S. Capital Police forcibly removing disabled demonstrators from a protest over the Senate’s now-defunct health care bill. Nobody wants their business to be featured in similar reporting.
Of course, things are rarely simple when it comes to government regulations and the ADA is no different. Complicating the landscape is HR 620, the “ADA Education and Reform Act of 2017,” currently making its way through Congress. According to the Center for American Progress the bill, sponsored by Rep. Ted Poe (R-Texas), would require anyone seeking to file a lawsuit against a business for ADA violations to first provide written notice to that business, outlining the provisions of the law that apply to the violation. Business owners would then have 60 days to acknowledge the violation and another 120 days to at least make “substantial progress” towards rectifying it.
Opponents of the bill claim it would gut enforcement of the ADA by allowing businesses to stall the correction of violation for months or years, while those in favor say it would prevent the “drive-by lawsuits” that end up forcing business owners to pay settlements to lawyers who make a career out of filing ADA suits. The ADA bars the awarding of monetary damages in successful lawsuits, but does allow the awarding of “a reasonable attorney’s fee.”
Meeting the challenge
In an effort to sort through the confusion over ADA guidelines, kiosk deployers are taking their own steps to accommodate disabled users.
The easiest steps to take are those that offer access to individuals in wheelchairs or who are otherwise vertically challenged. That includes offering at least one kiosk with adjustable height or a lower point of access.
“Swiveling mounts or adjustable height mounts may assist in accessibility – but they don’t solve the problem just by being available,” said Laura Miller, director of marketing with York, Pa.-based KioWare Kiosk Software.
“The physical placement of the kiosk is just as important as the presence of accessibility features and testing is needed even with the purchase of an accessible kiosk,” she said. “If the path to the kiosk is too narrow to approach head on, for instance, it becomes moot that the kiosk itself is accessible because getting to the kiosk is too challenging or the space too constricted. Vertical and horizontal reach must be considered.”
As mentioned earlier, though, making the kiosk available to those in a wheelchair isn’t enough.
“No longer can you get away with a kiosk just being ‘reachable’,” said Frank Olea, CEO of Cerritos, Calif.-based Olea Kiosks. “Most companies will say their product is ADA compliant, but they fail to mention they’ve only covered a very small spectrum of individuals with disabilities. Sure, someone in a wheelchair can reach the screen, but serving people with disabilities goes far beyond that.”
As demonstrated by the Eatsa scenario, one of the biggest challenges in deploying interactive self-service technology is accommodating visually impaired users. A touchscreen relies heavily on users being able to see the screen, so deployers need to find ways to communicate that information in other ways.
“Without access to speech feedback for on screen contents and a method for determining what item the user is activating, a person who is blind or visually impaired cannot effectively make use of a touchscreen or tablet based kiosk,” said staff at the American Foundation for the Blind.
“For those with low vision, small or ornate fonts are difficult, if not impossible, to read,” AFB officials said. “Low contrast between the foreground and background can also make on-screen and print-labeled items difficult to read.”
In addition, glare on the screen and on any print-labeled areas of the machine can cause readability barriers for people with low vision, the AFB said.
“What I advise people to do is to recreate a version of the kiosk software that can be used by people with visual problems,” said Mike James, CEO of Washington D.C.-based Kiosk Group Inc.
“Information can be presented in large text and contrasting colors for people who are marginally blind, and to have a system for audio feedback for those who are completely blind,” James said. Those prompts can be used in conjunction with Braille keyboards to assist with navigation.
Accommodating users with hand mobility issues is a concern as well. An ‘Automated Passport Solution’ Olea built for deployment in the Dallas Fort Worth Airport incorporates the Nav-Pad, a keypad designed by London-based Storm Interface that provides accessibility to a kiosk’s functions for those with physical or sensory impairments. The APS kiosk shortens the clearance process for international travelers by collecting biographical and passport information from passengers before they are seen by a customs officer.
The Nav-Pad, developed in partnership with the Trace Research & Development Center, was originally designed for use in military and industrial applications where the user might be wearing heavy gloves. One of the pioneers in the space, Storm Interface also offers the Audio-Nav Keypad, an assistive USB device offering menu navigation by means of audio direction.
The work continues
As ADA compliance becomes a bigger and bigger issue for hardware manufacturers, software developers and kiosk deployers, a variety of industry groups are working to develop solutions that can meet the needs of disabled users.
The Kiosk Industry Association, for example, has formed an ADA working group and committee expressly for ADA to try and standardize guidelines for the industry. A big initiative for the association is meeting with the US Access Board directly to help communicate industry information and context to the standards body directly.
Other organizations with ADA initiatives include the Electronic Transactions Association, which has also formed a working group. The ETA represents more than 500 companies worldwide involved in electronic transaction processing products and services, working to influence, monitor and shape the payments industry by providing leadership through education, advocacy and the exchange of information.
“The purpose of the group is to promote compliance and the development and deployment of products and services to help ensure access to the payment system,” said Meghan Cieslak, ETA’s director of communications. “The group is comprised of industry experts, start-ups, as well as ISOs and VARs – all focused on helping disabled Americans access the payment system.”
The Kiosk Industry Association is consulting with the ETA on access initiatives and has also enlisted the assistance of the ATM Industry Association which already has a formal ADA document via EFTA for their members.
It’s also critical for deployers to think about accessibility from the very beginning of a kiosk project. A paper co-authored by Peter Jarvis and Nicky Shaw, both from Storm Interface, along with Robin Spinks from the U.K.’s Royal National Institute of Blind People (RNIB) included the following recommendations:
“Accessibility is most effectively achieved when adopted as a primary system specification,” the group wrote.
“It is most successfully implemented if considered during the concept design process,” they wrote. “Accessibility should be a primary objective during the origination of hardware solutions, application software and content to be delivered.”
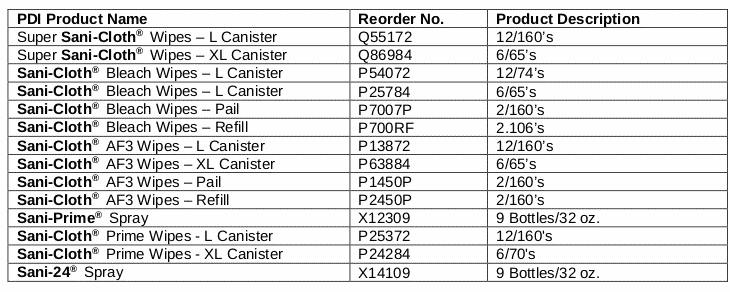
In addition, consideration should also be given to the environment in which the system will be installed, they wrote, and that terminals located in public or unsupervised environments will need to survive regular cleaning and sanitization procedures using sprayed liquid disinfectants and other cleaning agents.
Along with providing hardware designed for accessibility, the application or website on the kiosk must be built with more than a cursory nod toward compliance in order to have these other components “work” in a successful and accessible deployment. The kiosk system software can utilize accessibility features and the hardware can provide sound, include keyboards and be height adjustable, but if the application isn’t built with accessibility in mind, or modified to make sure accessibility features are fully integrated, usability and accessibility will suffer for it.
These concerns, and others, are driving the various partnerships on ADA issues.
“It was pretty much a no-brainer for us to go ahead and work together on standardizing,” Keefner said.
“I’ve been really passionate about it and I’ve talked to kiosk manufacturers about binding together to create standards on kiosk design so people who walk up to a kiosk know where to find the audio jack, know where to find the braille keyboard or whatever,” said Kiosk Group’s Mike James. “Those features could be the same for every project.”
Unfortunately, despite the additional clarification on access rules it’s likely that in the short term it’s likely that many compliance issues are likely to be hashed out in court.
“It seems that there are a few people out there who have made it their job to litigate any non-ADA-compliant situations that arise,” Miller said. “This is not exclusive to kiosks, but they have not been completely spared, and while it seems relatively obscure at this point, those individuals looking for violations will likely eventually hit on the existence of kiosks as fodder for their litigious pursuits.”
Resources for kiosks and ADA compliance
ADA Committee and ADA Working Group for Kiosk Association
ADA White Paper on Kiosk Industry
Access Board final rule for information and communication technology
Trace Research and Development
National Council on Disability Report
Interactive Accessibility – accessibility consulting firm
Digital Business kiosk consultants
COMMENTS
Richard and Craig
I wanted to congratulate you both on an excellent and informativearticle. Thank you for helping to bring the importance of ADA and ACAA mandates to the attention of the Kiosk Industry and to those agencies deploying and operating ICT in public environments. Thanks also for recognizing Storm Interface in the text of the article and for including some of those images showing deployed installations. We are constantly working to improve and add to the range of accessibility and assistive technology products available to kiosk designers. There are some exciting new developments in process which will help to deliver the “multi-modal” methods of system interface that are widely predicted to be the next big step in system accessibility. The priority will be to ensure our partners in the kiosk industry are kept aware of and fully supported in the deployment of Assistive Technology Products (ATP).
Hopefully your article will receive the recognition it deserves and I will have an opportunity to work with you both to maintain awareness of accessibility issues within the kiosk industry.
Best Regards
Peter Jarvis
Senior Executive VP